28 June, 2023 by Mehul Srivastava
When Progress Corp, the Massachusetts-based maker of business software, revealed its file transfer system had been compromised this month, the issue quickly gathered global significance.
A Russian-speaking gang dubbed Cl0p had used the vulnerability to steal sensitive information from hundreds of companies including British Airways, Shell and PwC. It had been expected that the hackers would then attempt to extort affected organisations, threatening to release their data unless a ransom was paid.
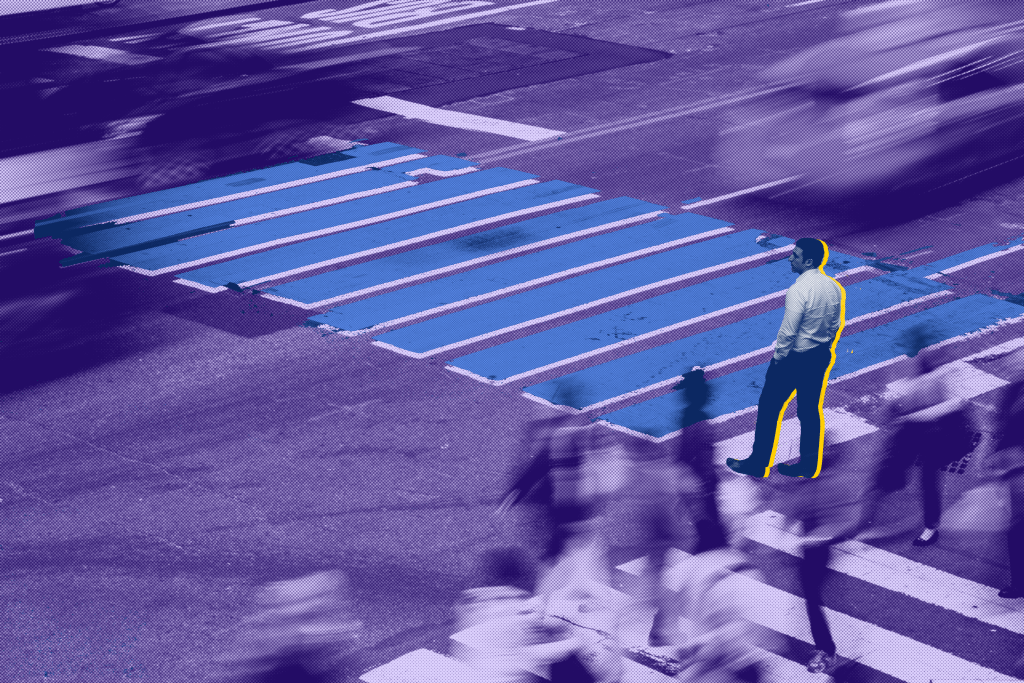
However, cyber security experts said that the nature of the data stolen in the attack — including the driving licenses, health and pension information of millions of Americans — hints at another way hackers would cash in: ID theft scams, which combined with the latest in so-called deepfake software may prove even more lucrative than extorting companies.
“I am not a criminal, but I’ve been studying this for a long time — if I had this much information, and it was so pristine, the sky is the limit,” said Haywood Talcove, the chief executive of LexisNexis Risk Solutions’ Government division.
Experts have long warned about the growth of deepfake scams where criminals pair artificial intelligence software with personal information to create realistic digital likenesses of people to bypass traditional security checks.
The number of deepfakes used in scams in just the first three months of 2023 outstripped all of 2022 and then some, according to Miami-based Sumsub, a verification platform, with particularly high growth in Canada, the US, Germany and the UK.
This is because faking a western citizen’s identities unlocks not just bank and traditional online scams, but also the theft of government benefits.
For example, Talcove said the sort of information stolen in the Progress hack — photographs, names, dates of birth, home addresses and parts of their social security numbers — could be used to create fake video selfies that many US state agencies use to verify identities.
That could allow criminals to successfully claim unemployment benefits, and apply for federal college loans, food stamps and other programs. He estimated each stolen identity can be successfully leveraged to steal as much as $2mn just from government benefit programs alone.
“As AI advances, more tools become available to fraudsters . . . the use of synthetic fraud is rising at an alarming rate,” said Pavel Goldman-Kalaydin, at Sumsub, who says the company has to keep coming up with new ways to spot these sophisticated fakes.
On June 1, after at least one of its customers had their data breached, Progress revealed that hackers had found a previously undiscovered weakness in its software that allowed them to target its clients.
The breach eventually led to the theft of terabytes of data from Progress’s customers including oil company Shell and accounting rivals PwC and EY, as well as dozens of other American government agencies, including the Department of Agriculture, Maryland’s health services and the California pensions system, one of the largest in the world.
The sprawling landscape of victims — many of whom are yet to publicly acknowledge the breach — are connected to each other by their reliance on a piece of software called MOVEit, made by Progress, which was advertised as a secure method for companies to comply with data processing regulations, keeping their most precious information safe both in transit and in storage.
The second part of the heist was expected to be extortion: demanding payment or leaking the data is put on the dark web. For instance, the hackers recently posted a vast amount of data from Shell, an indication that the company did not pay a ransom. Shell said a very small number of its employees used the software, and the rest of its systems were untouched.
“This was not a ransomware event,” the company said. “There is no evidence of impact to any other Shell IT systems. Our IT teams are investigating.”
The hackers, who declined via email to comment, also leveraged a highly sophisticated webshell, or backdoor, that appears to have bypassed industry-standard security measures from companies like Microsoft or CrowdStrike, according to two people familiar with the initial investigation into the hack.
Progress said it was working with law enforcement and helping its customers further secure their data, “including applying the patches we have released”.
“We are committed to playing a leading and collaborative role in the industry-wide effort to combat increasingly sophisticated and persistent cybercriminals intent on maliciously exploiting vulnerabilities in widely used software products,” the company said.
Progress is relying on Charles River Associates, a consultancy, the forensics division of DLA Piper, the law firm, and Google-owned Mandiant cyber security as it prepares for lawsuits against it.
The US Cybersecurity and Infrastructure Security Agency did not reply to multiple requests for comment.
Louisiana and Oregon’s governors have held emergency discussions on the hack and told citizens to freeze their credit, change all their passwords and keep an eye on their benefits accounts.
“Organised crime syndicates, state operations, and professional fraud groups are those most likely to use this information . . . with the intent of committing global ID fraud at scale,” said Ron Atzmon, founder of AU10TIX, an Israel-based company that counts Google, Microsoft, PayPal and LinkedIn among it clients for identity verification.
Since the data stolen was real, he said, “it will be verified as genuine when fraud is attempted, allowing it to pass through most case-level checkpoints”.
He added: “We believe that in the coming months we will see an uptick in serial fraud attacks across the board due to the influx of stolen identity information getting into the hands of professional fraudsters.”
At the California Public Employees’ Retirement System, or Calpers, the Cl0p hackers made off with the personal data of about 769,000 retired members and their survivors. The data of recently deceased Americans was particularly valuable in the black market, said a private cyber security official involved in investigations at several victims.
“You open a credit card in a dead man’s name, take out loans, redirect social security payments, sign up for food benefits,” the person said. “Who’s going to ring the alarm?” he said.
© The Financial Times Limited 2023. All Rights Reserved.
FT and Financial Times are trademarks of the Financial Times
Ltd. Not to be redistributed, copied or modified in any way.